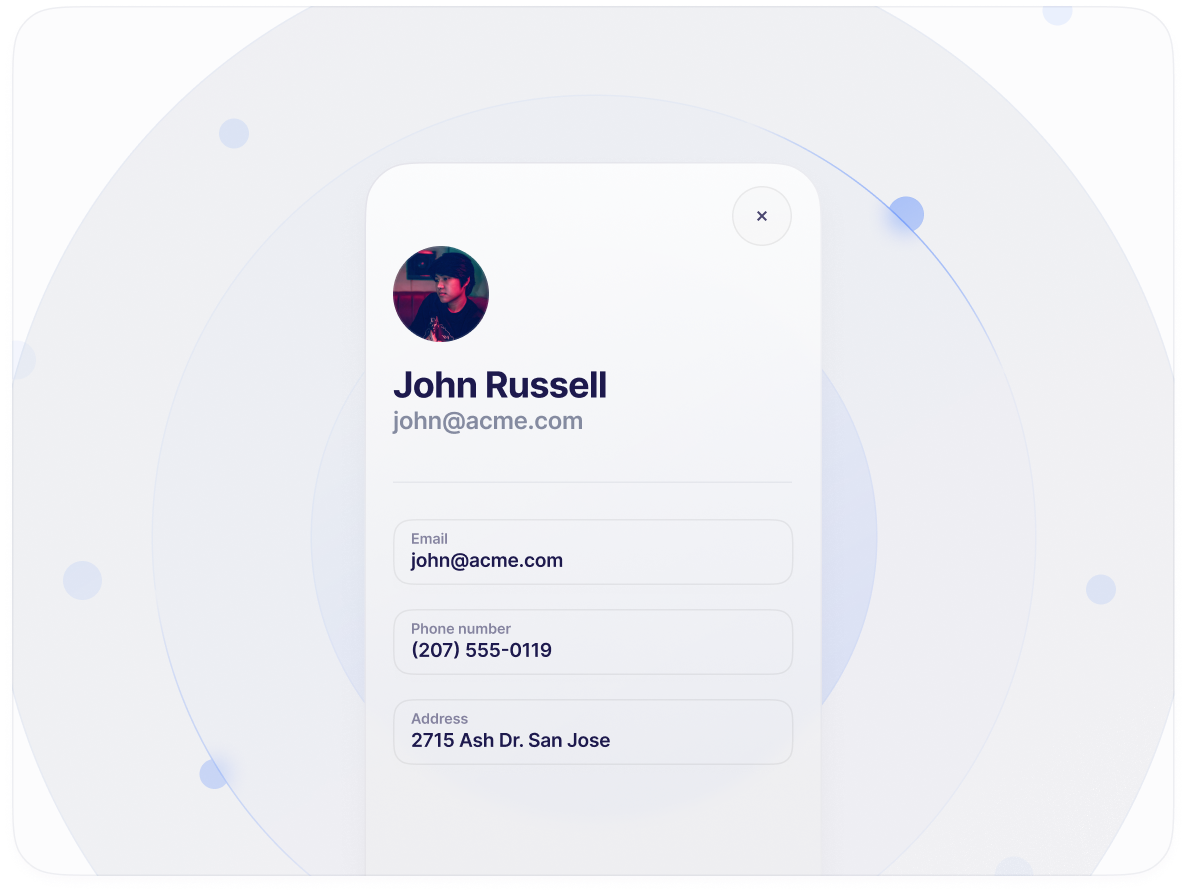
Secure user data
Multi-region and exfiltriation-resistent
SlashID is the only IdP that is natively multi-region and implements application-layer encryption with a hardware root of trust, solving compliance needs and avoiding data breaches.
Control breaches
Reduce data breaches blast radius.
Secured accounts
Prevent credential stuffing and phishing.
Risk-base authentication
Step up user flow auth for critical operations.
Offload security
Improve user data protection, reduce cost.
Build confidence
Increase customers’ trust.
Captcha free
Detect bots without human verification walls.