Detect real threats & close hidden gaps across your entire identity attack surface
Combined identity threat detection and security posture management, powered by an AI engine that evaluates live behavioral data against your full identity graph to surface the risks that actually matter.
Siloed tools generate alerts without context. Attackers move faster than your team can correlate events across IdPs, cloud, SaaS, and on-prem.
SlashID combines identity threat detection with continuous posture management in a single platform — the AI engine evaluates behavioral signals against full identity graph context to surface real threats, suppress noise, and close the loop with automated remediation.
Detect what’s real
500+ built-in detections powered by an AI engine that evaluates live behavioral data against identity graph context. Real threats surfaced, noise suppressed.
See every gap
Continuous posture management across human, non-human, and AI agent identities. Misconfigurations, policy drift, and toxic permission paths surfaced before attackers or auditors find them.
Remediate in the same workflow
One-click or automated response: enforce MFA, suspend accounts, rotate credentials, revoke sessions. Orchestrate through SlashID or your existing SIEM/SOAR.
Benefits
How it helps
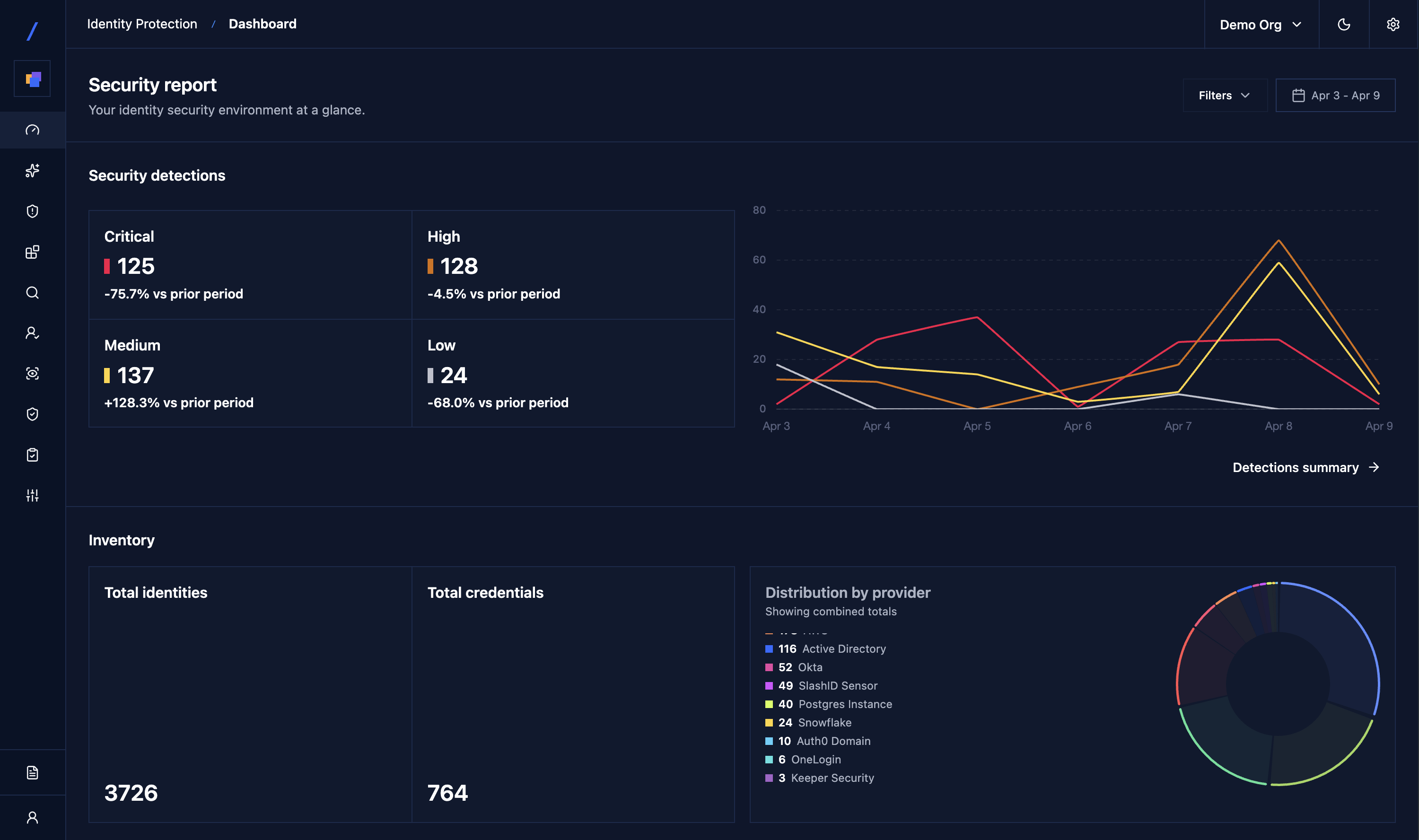
AI-powered detection, evaluated against live context
The AI engine evaluates 500+ detection rules against live behavioral data and full identity graph context — ATO, push-bombing, lateral movement, privilege escalation, Kerberoasting, token theft, posture drift, and more. Findings are scored by blast radius and correlated across environments, not fired as raw alert volume. Your team investigates real threats, instead of chasing down alerts.
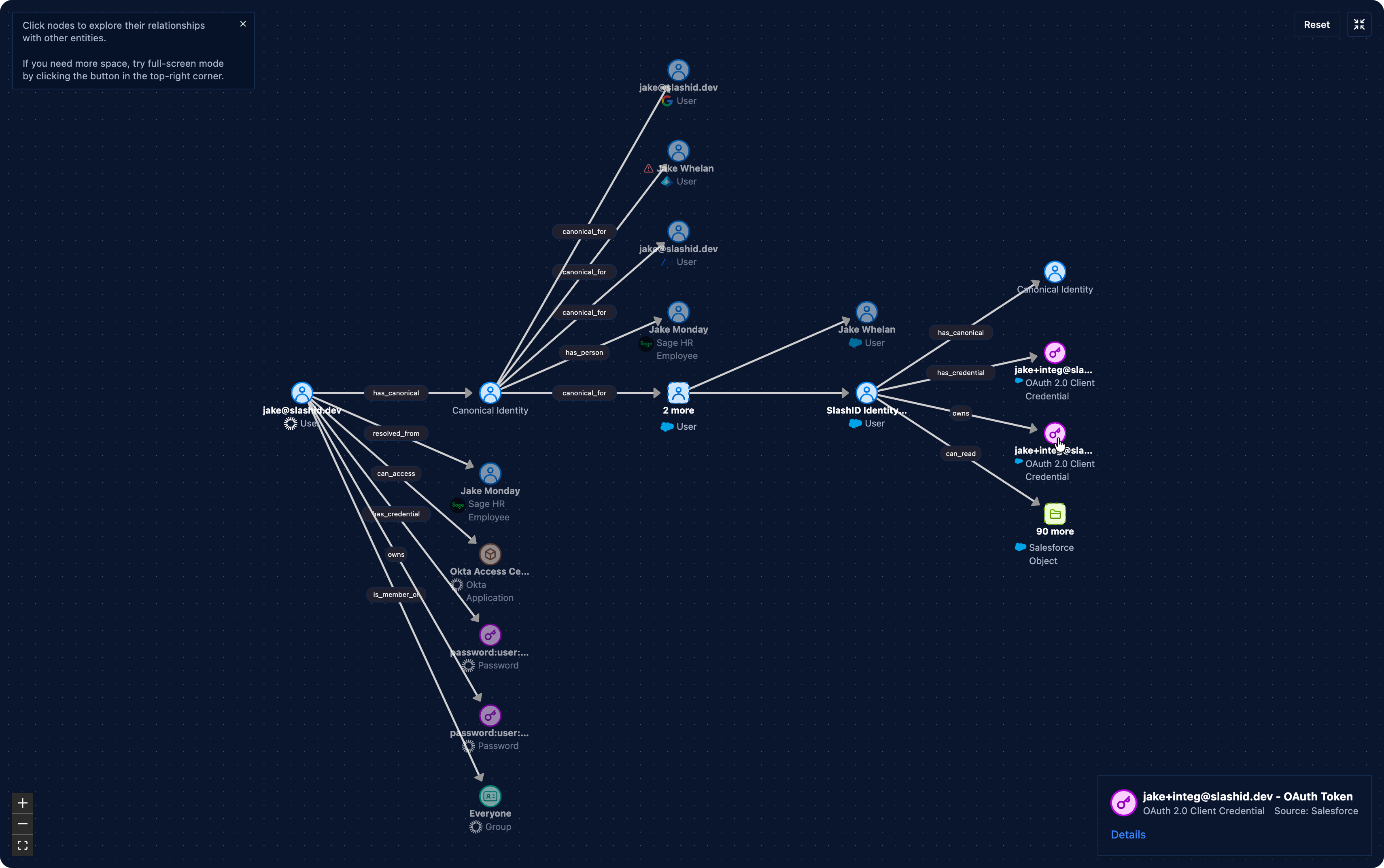
Unified access graph across every environment
Human identities, non-human identities, and AI agents mapped across cloud, SaaS, on-prem, and browser — with full entitlement and permission context. One inventory, not ten consoles. The graph is the shared context layer that powers both detection and posture.
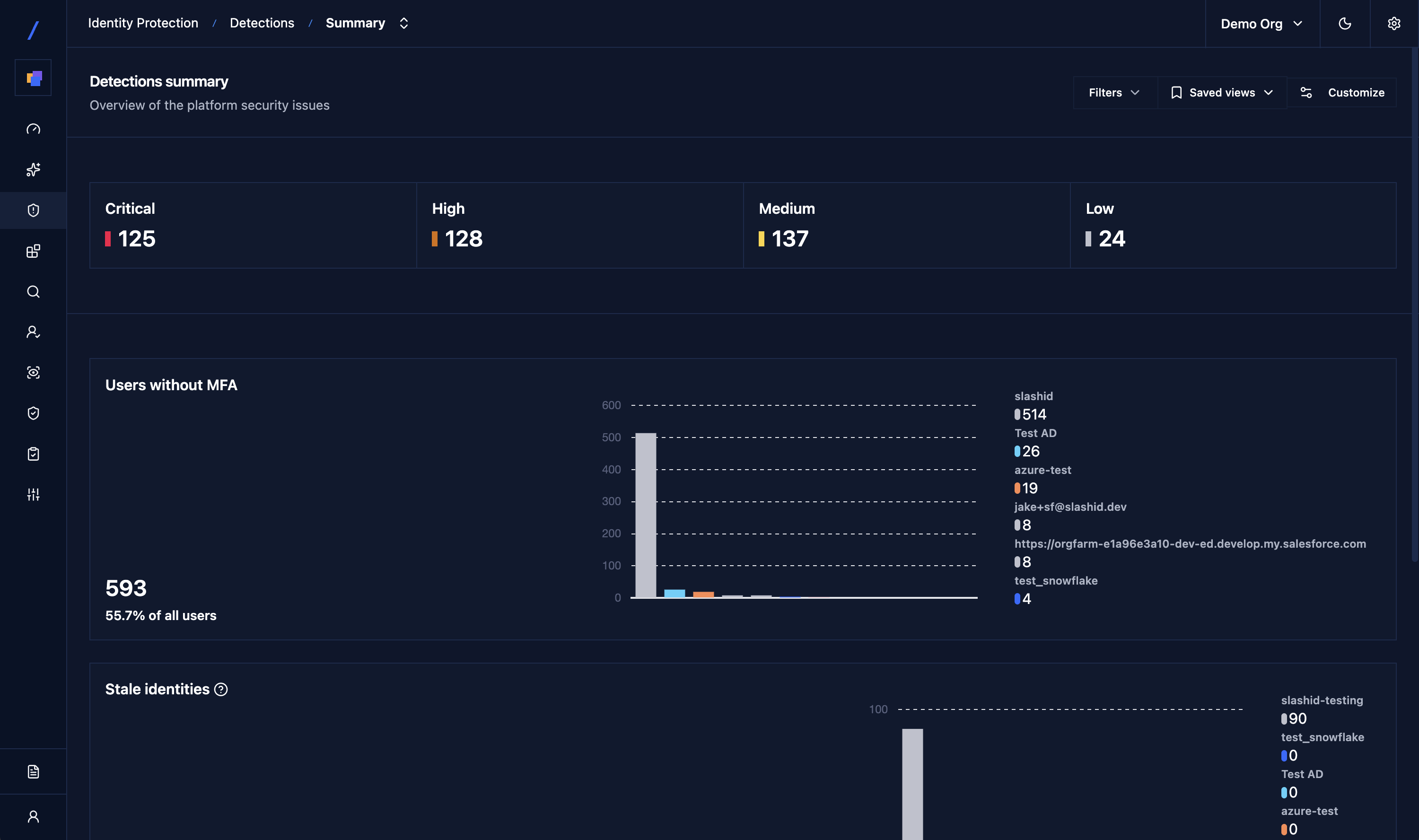
Continuous posture management
Surface misconfigurations, missing MFA, SoD violations, stale credentials, shadow SaaS, and toxic permission paths the moment they appear. Drift alerts fire when new changes break guardrails — not at the next quarterly review.
Non-human identity & AI agent coverage
Discover and monitor service accounts, API keys, OAuth tokens, and AI agent permissions. Behavioral detection catches anomalous NHI activity that traditional tools miss entirely.
Browser-layer phishing and session protection
Stop credential theft, AiTM attacks, and session hijacking in real time at the browser — before stolen tokens reach your identity infrastructure. Shadow SaaS discovery and enforcement included.
Remediation workflows that close the loop
Enforce MFA, suspend accounts, rotate credentials, revoke sessions, open IR tickets with full context. Orchestrate through SlashID’s APIs, workflow engine, or your SIEM/SOAR. Guided one-click actions for manual response, automated playbooks for everything else.
Easy to deploy
How it works
Read-only connectors stream identity data from IdPs, cloud providers, SaaS apps, on-prem environments, and browser extensions.
SlashID correlates identities, entitlements, configurations, and behavioral signals into a unified access graph — the shared context layer that powers both detection and posture.
The AI engine evaluates detections against live behavioral data and graph context. Findings are scored by blast radius, not raw alert volume.
Fix issues through guided one-click actions, automated playbooks, or API-driven orchestration to your existing SIEM/SOAR stack.
Unique Product Core
Access Graph Engine
- Unified identity graph — humans, non-human identities, AI agents, every resource and entitlement
- Cross-environment visibility across cloud, SaaS, on-prem, and browser
- Deep queries reveal SoD violations, privilege creep, and toxic role paths
AI-Powered Detection & Response
- 500+ out-of-the-box detections with AI evaluation against live behavioral data and identity graph context
- Behavioral detection for ATO, lateral movement, insider misuse, and NHI anomalies
- Automated remediation via workflow engine, APIs, or native SIEM/SOAR integration